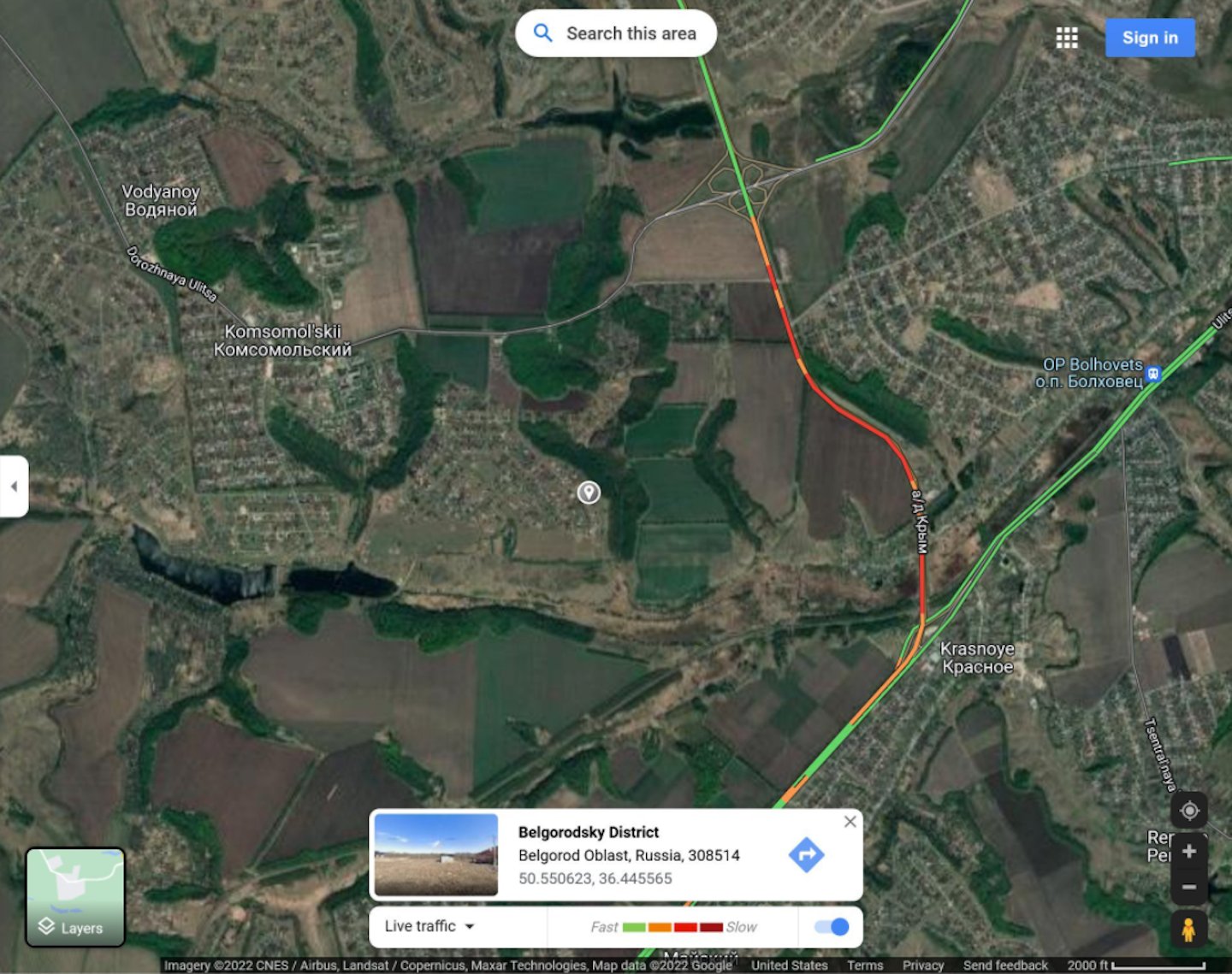
At 3:15 in the morning on 24 February 2022, a traffic jam appeared on Google Maps on a rural road near Belgorod, Russia — heading south toward the Ukrainian border. No spy satellite triggered the alarm. No classified intelligence was exchanged. A professor at the Middlebury Institute of International Studies spotted the anomaly on a free app, posted a single tweet — "Someone's on the move" — and roughly an hour later, Russia began its full-scale invasion of Ukraine.
The entire early warning came from a tool available on any smartphone.
That moment marked a turning point — not just in warfare, but in how intelligence itself works. For the first time, a global conflict played out in near real-time, visible to anyone with the right tools and the knowledge to read what they were seeing. The implications extend well beyond the battlefield.
The Pattern Repeated: Iran, 2026
Four years later, the playbook ran again. In February 2026, as US-Iran tensions reached a breaking point over Tehran's nuclear programme, the world did not need a leaked Pentagon briefing to understand what was coming. They had FlightRadar24.
Civilian OSINT analysts watching the publicly available flight-tracking platform observed something unmistakable: dozens of KC-135 Stratotankers and KC-46 refuelling aircraft departing US bases in America and the UK, heading east. F-22 Raptors. F-35s. E-3 Sentry AWACS aircraft. Cargo transports moving personnel and equipment at a tempo inconsistent with routine rotations. Over 120 aircraft repositioned to the region within days — the largest surge of US airpower in the Middle East since the 2003 Iraq War. No official statement was issued. The US Department of Defense said nothing. The picture was already assembled, entirely from public flight data, by people at their desks.
What OSINT Actually Is
Open-source intelligence — OSINT — is the collection and analysis of publicly available information. Not hacking. Not covert surveillance. Traffic data. Flight tracking. Satellite imagery. Company registrations. Job listings. Social media. Court records. Domain registrations. It is all legal, all open, and increasingly all automated.
These conflicts transformed OSINT from a niche intelligence discipline into a mass-participation activity. Investigators used commercial satellite imagery to track Russian convoy movements. Ukrainian civilians reported troop positions via smartphone. A Russian submarine commander was located — and later killed — after posting his jogging routes on Strava. Russian soldiers' TikTok videos exposed unit types, convoy routes, and vehicle formations to open-source analysts worldwide. The digital footprint of a military operation proved nearly impossible to conceal, even from people with no intelligence training and no budget.
What These Conflicts Proved
- Google Maps traffic data predicted the Ukraine invasion before it began
- Commercial satellite imagery exposed 40-mile Russian convoys in real time
- FlightRadar24 revealed the scale of America's Iran military buildup before any official statement
- A Russian submarine officer was geolocated and killed via his public fitness app data
- Soldiers' social media posts exposed unit types, routes, and formations to open-source analysts
The Bridge to Australian Business
Here is the question that matters for every Australian organisation: if the world's most powerful militaries cannot conceal their movements from people using free tools, what makes you think your business can?
The same techniques that predicted an invasion and exposed a military buildup are applied to Australian companies every day — by competitors conducting market intelligence, by threat actors mapping attack surfaces, by journalists investigating stories, by regulators conducting due diligence, and by activists researching targets. The tools are identical. The data is the same. Only the objective differs.
Your organisation has a digital footprint whether you have managed it or not. That footprint includes your infrastructure, your technology stack, your staff's online presence, your historical domain registrations, your exposed credentials from third-party breaches, and the gap between what your privacy policy says and what your systems actually do. All of it is publicly accessible. All of it tells a story to anyone who knows how to read it.
What This Means in Practice
The business parallels are direct. A competitor monitoring your job listings sees a hiring surge in a specific capability area weeks before any market announcement — the corporate equivalent of a traffic jam at 3am. A threat actor tracking your infrastructure identifies a legacy subdomain running vulnerable software you forgot existed. A journalist finds court records, ASIC filings, and archived news that paints a picture your communications team has never considered. A regulator reviews your public-facing website and identifies data collection practices not disclosed in your privacy policy.
None of this requires sophisticated capability. It requires only the knowledge of where to look — which is, increasingly, the only barrier that remains. Australia-based OSINT Combine, founded by an ADF veteran and now trusted by ASX 200 companies and national intelligence agencies, has built an entire industry around this reality. The 2024 Australian Independent Intelligence Review identified open-source intelligence and economic security as national priorities. The global OSINT market, valued at $12 billion in 2025, is projected to exceed $127 billion by 2034. What was once a military discipline is now standard business practice.
Three Things To Do Right Now
Search yourself like a threat actor would. Run your domain, your key executives, and your company name through the same tools a hostile researcher would use. What appears? What has been indexed that you never intended to make public? What does the picture say about your organisation to someone who has never spoken to you?
Understand your suppliers' exposure. The Belgorod traffic jam was visible because large movements leave large traces. Your supply chain partners leave traces too — financial stress, compliance failures, security gaps — all visible in their public footprint, all transferable risk to your organisation.
Commission a passive assessment. The most effective way to understand your external exposure is to have it assessed by someone who knows what they are looking for. A structured passive OSINT assessment maps your complete footprint — infrastructure, domains, credentials, technology stack, compliance posture — and presents it the way a threat actor would see it, before they get there first.
The lesson from Ukraine and Iran is not that OSINT is a military curiosity. It is that publicly available information, read correctly, reveals everything about an organisation's vulnerabilities and position — long before that organisation is aware it has been read at all. The only variable is whether you have read your own organisation first.